Keeping software libraries up to date can feel like trying to clean your room during a windstorm. You fix one thing, and three more get messy. That is where dependency update software comes in. It helps automate the process of updating libraries in your projects. And yes, it can save you from hours of boring manual work.
TL;DR: Dependency update software automatically checks for outdated libraries and updates them for you. It saves time, reduces security risks, and keeps your code healthy. These tools can create pull requests, run tests, and even fix version conflicts. If you build software, you probably need one.
What Are Dependencies?
Let’s start simple.
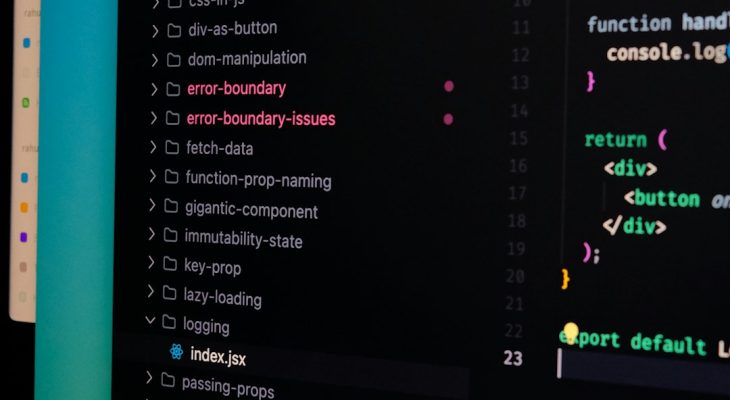
When you build software, you rarely write everything from scratch. You use external code packages. These are called dependencies. They are libraries that handle common tasks like:
- Sending web requests
- Working with databases
- Handling authentication
- Designing user interfaces
- Logging and monitoring
Think of dependencies like ingredients in a recipe. You do not grow your own wheat to make bread. You buy flour. In the same way, developers “buy” code from package managers.
Common package managers include:
- npm for JavaScript
- pip for Python
- Maven for Java
- NuGet for .NET
But here is the catch. These libraries change. A lot.
The Problem With Outdated Libraries
Libraries get updated for many reasons:
- Security fixes
- Bug fixes
- Performance improvements
- New features
If you do not update them, bad things can happen.
Your app might:
- Have security vulnerabilities
- Break when other systems change
- Run slower than needed
- Miss out on useful features
Now imagine you have 50 dependencies. And each has updates every few weeks. That is a lot to track manually.
This is where automation becomes your best friend.
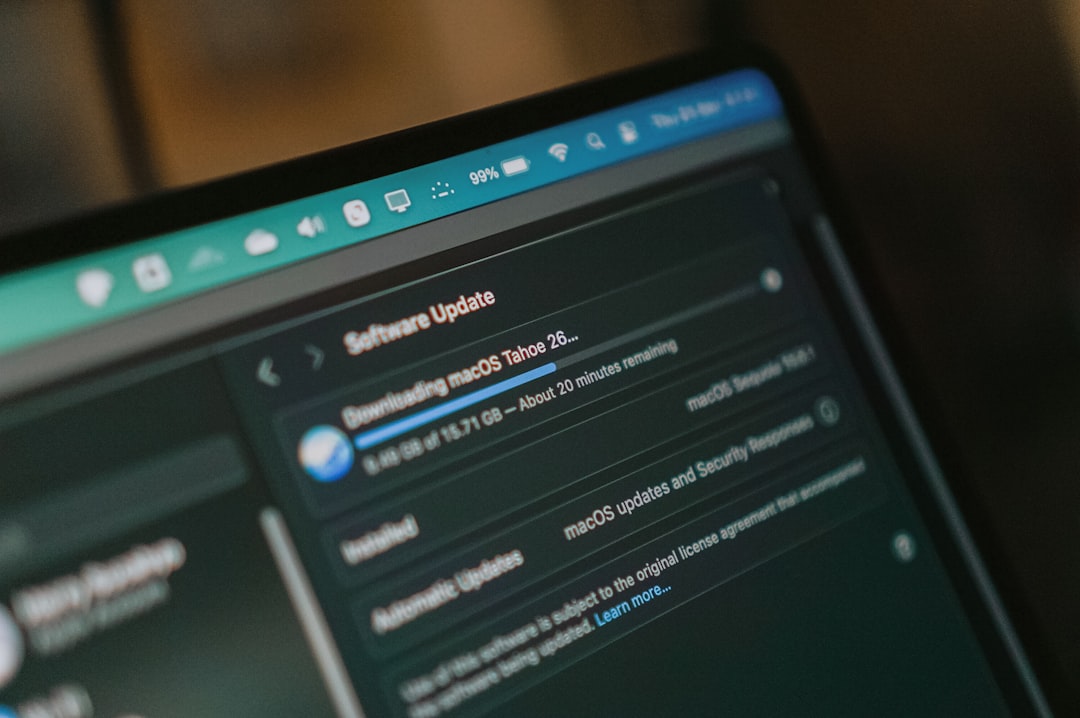
What Is Dependency Update Software?
Dependency update software is a tool that:
- Scans your project
- Detects outdated libraries
- Checks for known vulnerabilities
- Suggests or applies updates automatically
Some tools even go further. They create pull requests in your Git repository. They run your test suite. They check if anything breaks. Then they ask you to review and approve.
It is like having a junior developer who only works on library updates. And never gets tired.
How It Works (In Simple Terms)
Here is the basic flow:
- The tool reads your dependency file. For example, package.json or requirements.txt.
- It compares your versions with the latest available versions.
- It checks vulnerability databases.
- If an update is needed, it creates a change.
- It runs automated tests.
- It opens a pull request for you to review.
You then review the change, merge it, and move on with your life.
Magic. But very practical magic.
Popular Dependency Update Tools
There are several well-known tools in this space. Each has its own style.
- Dependabot – Deep integration with GitHub. Very popular.
- Renovate – Highly configurable. Works with many ecosystems.
- Snyk – Focused heavily on security vulnerabilities.
- Greenkeeper – Historically known in the JavaScript world.
Most of these tools support multiple languages and package managers. So you can use them across different projects.
Why Automation Matters
Manual updates sound simple. But in real life, they are not.
Here is what manual updating looks like:
- You check for outdated packages.
- You update them one by one.
- You read changelogs.
- You fix breaking changes.
- You run tests.
- You repeat next week.
Now multiply this by 10 projects.
Automation helps because:
- It runs on a schedule.
- It never forgets.
- It scales across projects.
- It reduces human error.
You spend less time babysitting dependencies. And more time building features.
Security Benefits
One of the biggest reasons to use dependency update software is security.
Many cyber attacks exploit known vulnerabilities in outdated libraries. Not fancy new hacks. Just old bugs that were never patched.
That is scary.
Dependency tools often connect to vulnerability databases. For example:
- National Vulnerability Database
- GitHub Security Advisories
- Vendor security feeds
When a vulnerability is found in one of your libraries, the tool alerts you. Some tools even create an emergency pull request.
This shortens the window between “vulnerability discovered” and “fix deployed.”
That can make a huge difference.
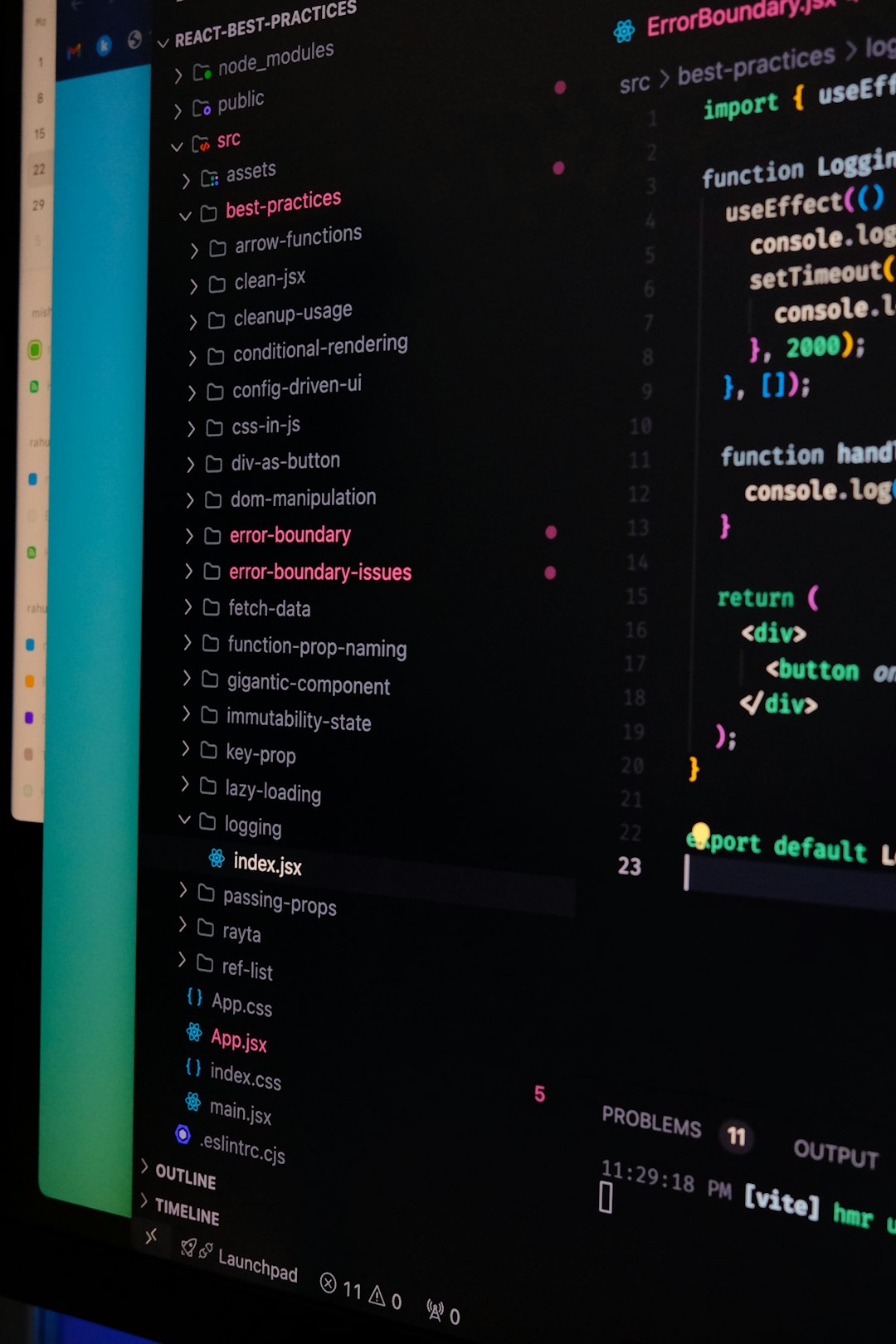
Handling Breaking Changes
Not all updates are simple.
Libraries follow versioning systems. Often something called Semantic Versioning. You may have seen versions like:
2.4.1
- First number: Major version
- Second number: Minor version
- Third number: Patch version
Patch updates are usually safe. Minor updates sometimes add features. Major updates can break your code.
Good dependency tools understand this. They can:
- Group minor and patch updates
- Separate major updates
- Schedule risky upgrades less frequently
This keeps your team from being overwhelmed.
Best Practices for Using Dependency Update Software
Just installing the tool is not enough. You need a strategy.
Here are some smart practices:
- Enable automated tests. No tests, no safety net.
- Limit the number of open update pull requests. Too many creates noise.
- Review changelogs for major updates. Do not merge blindly.
- Schedule updates during low traffic times. Reduce risk.
- Monitor after deployment. Watch for hidden issues.
Think of the tool as an assistant. Not a replacement for thinking.

Common Myths
Myth 1: “If it works, do not touch it.”
This mindset leads to giant, painful upgrades later. Small, regular updates are easier.
Myth 2: “Automation will break everything.”
Actually, small automated updates are safer than rare massive upgrades.
Myth 3: “We are too small to need it.”
Even solo developers benefit. Especially solo developers. You have less time to waste.
Challenges to Be Aware Of
Dependency update software is not perfect.
You may face:
- Noisy pull requests
- False positive security warnings
- Complex version conflicts
- Breaking changes in major upgrades
But these are manageable. And far less painful than ignoring updates for two years.
The Bigger Picture: Healthy Codebases
A healthy project has:
- Up-to-date dependencies
- Automated tests
- Continuous integration
- Security monitoring
Dependency update software fits neatly into modern DevOps practices. It works alongside CI pipelines. It supports continuous delivery. It encourages small, frequent improvements.
Over time, this creates stability.
Your project becomes easier to maintain. Easier to onboard new developers. Easier to scale.
Is It Worth It?
Short answer: almost always yes.
The benefits include:
- Saved time
- Improved security
- Fewer surprise breakages
- More predictable upgrades
The cost is usually small. Many tools have free tiers. Setup is often simple. Especially if you already use platforms like GitHub or GitLab.
And once it runs, it mostly takes care of itself.
Final Thoughts
Software moves fast. Libraries evolve daily. Security issues appear without warning. Trying to manage all of this manually is like using a paper map in a GPS world.
Dependency update software gives you visibility. It gives you automation. It gives you consistency.
It will not write your application for you. But it will keep its foundations solid.
And that peace of mind? That is priceless.